Kubernetes Best Practices - Part 1 - Small Base Images
The first step in deploying to Kubernetes is putting your app inside a container. Let's explore how you can create small and secure container images.
Before that, a big thanks to docker, creating container images has never been simpler. With docker you just specify your base image, add your changes, and you can build your container.
Base Images
While this is great for getting started, using the default base images can lead to large images full of security vulnerabilities. Most Docker images use Debian or Ubuntu as the base image. While this is great for compatibility and easy onboarding, these base images can add hundreds of megabytes of additional overhead to your container.
For example, simple Node.js and Go, "hello world" apps are around 700 megabytes. Your application is probably only a few megabytes in size. So all this additional overhead is wasted space and a great hiding place for security vulnerabilities and bugs.
Small base images
Using smaller base images is probably the easiest way to reduce your container size. Chances are your language or stack that you are using provides an official image that's much smaller than the default image.
For example, let's take a look at our Node.js container.
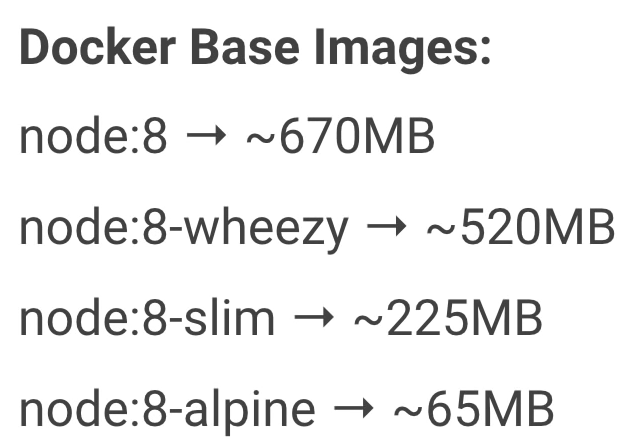
Going from the default node:8 to node:8-alpine reduces our base image size by 10 times.
To move to a smaller base image, update your Docker file to start with a new base image. Now, unlike the old "onbuild" image, you need to copy your code into the container and install any dependencies. For example,
FROM node:alpine
WORKDIR /app
COPY package.json /app/package.json
RUN npm install --production
COPY server.js /app/server.js
EXPOSE 8080
CMD npm startIn the above Docker file,
* The container starts with the node:alpine image
* Creates a directory for the code
* Install dependencies with NPM
* Finally, starts the Node.js server.
With this update, the resulting container is almost 10 times smaller. If your programming language or stack doesn't have an option for a small base image, you can build your container using raw Alpine Linux as a starting point.
This also gives you complete control over what goes inside your containers. Now, using a small base image is a great way to quickly build small containers. But you might be able to go even smaller using the builder pattern.
Security
People often say that containers are more secure if they're smaller, because they have less surface area for attacks. Let's see if this is actually true.
An awesome feature of Google Container Registry is that it can automatically scan your containers for vulnerabilities. This helps you identify and address vulnerabilities in the images stored in Google Container Registry.
In turn, this enables you to prioritize patching your images to other vulnerabilities, determine whether your environment is affected by a newly discovered vulnerability and ensure that your images are up to date and protected against the latest threats.
If we drill into the larger container, we can see that most of the issues have nothing to do with their app, but rather programs that we're not even using. When people talk about an increased surface area for attacks, this is what they're referring to.
"So remember to build small containers. The performance and security benefits are real."
